Intelligent Honeypot for Web Applications: Leveraging Seq2Seq and Reinforcement Learning
Main Article Content
Abstract
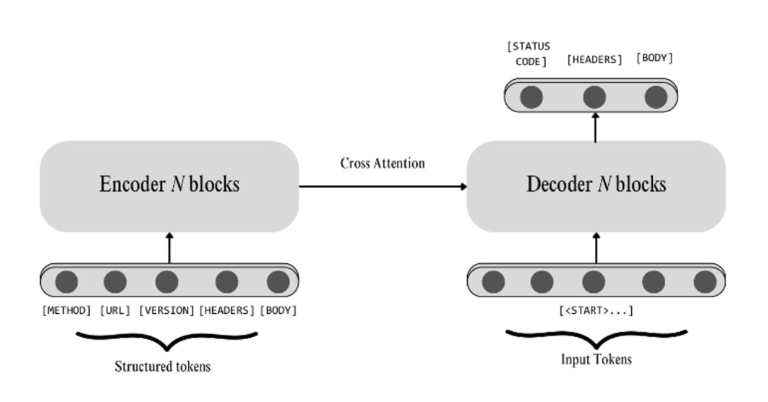
An intelligent honeypot system designed to mimic legitimate websites using Sequence-to-Sequence (Seq2Seq) learning and Deep Q-Learning. The system generates realistic, contextually appropriate responses to attacker queries, prolonging interactions and providing insights into malicious behaviors while safeguarding actual systems. The Seq2Seq model, trained on HTTP request-response pairs, enables the honeypot to produce responses that closely resemble those of real servers, enhancing its ability to deceive attackers. Deep Q-Learning optimizes engagement by selecting the most effective responses through a custom reward function, balancing realism and interactivity to maximize session length. Performance was evaluated using metrics such as Response Realism Rate (RRR), Semantic Consistency Accuracy (SCA), and Average Session Length (ASL). The honeypot achieved an RRR of 92.3%, an SCA of 89.7%, and a 94.5% Optimal Response Selection Rate (ORSR). These advancements increased ASL by 143.5%, from 3.2 to 7.8 exchanges, reflecting prolonged attacker engagement. By integrating Seq2Seq and Deep Q-Learning, this honeypot demonstrates significant improvements in generating convincing responses and sustaining interactions. These results contribute to modern cybersecurity by providing a practical and theoretical framework for developing next-generation honeypots capable of deceiving attackers and gathering actionable intelligence.
Article Details

This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.
References
D. S. Morozov, T. A. Vakaliuk, A. A. Yefimenko, T. M. Nikitchuk and R. O. Kolomiiets, “Honeypot and cyber deception as a tool for detecting cyber attacks on critical infrastructure,” 3rd Edge Computing Workshop. 81-96, 2023.
J. L. Zobal, D. Kol´aˇr and R. Fujdiak, “Current State of Honeypots and Deception Strategies in Cybersecurity,” 2019 11th International Congress on Ultra Modern Telecommunications and Control Systems and Workshops (ICUMT), Dublin, Ireland, pp. 1-9, 2019.
L. Huang and Q. Zhu, “Adaptive honeypot engagement through reinforcement learning of semi-markov decision processes,” 2019 10th International Conference on Decision and Game Theory for Security, Stockholm, Sweden, pp. 196-216, 2019.
Cobalt, “Cybersecurity statistics 2024,” 2024. [Online]. Available: https://www.cobalt.io/ blog/cybersecurity-statistics-2024.
Varonis, “Cybersecurity statistics,” n.d. [Online]. Available: https://www.varonis.com/ blog/cybersecurity-statistics.
L. Shi, Y. Li and M. Ma, “Latest Research Progess of Honeypot Technology,” Journal of Electronics Information Technology, Beijing, vol. 41, pp. 498-508, Feburary 2019.
I. Siniosoglou et al., “NeuralPot: An Industrial Honeypot Implementation Based On Deep Neural Networks,” 2020 IEEE Symposium on Computers and Communications (ISCC), Rennes, France, pp. 1-7, 2020. ´
G. Betarte, A. Pardo and R. Mart´ınez, “Web Application Attacks Detection Using Machine Learning Techniques,” 2018 17th IEEE International Conference on Machine Learning and Applications (ICMLA), Orlando, FL, USA, pp. 1065-1072, 2018.
D. Grunova, V. Bakratsi, E. Vrochidou and G. A. Papakostas, “Machine Learning for Anomaly Detection in Industrial Environments,” Engineering Proceedings, vol. 70, no. 1:25, 2024.
S. Chaudhari, A. Thakur and A. Rajan, “Securing Digital Information Using Cryptography Techniques to Enhance IT Security,” Research Reports on Computer Science, vol. 2, no. 3, pp. 13–22, 2023.
A. Onukrane, H. K. Skrodelis, G. Merkurjeva and A. Romanovs, “Navigating Web Application Security: A Survey of Vulnerabilities and Detection Solutions,” 2023 IEEE 64th International Scientific Conference on Information Technology and Management Science of Riga Technical University (ITMS), Riga, Latvia, pp. 1-6, 2023.
N. Provos, “Honeyd-a virtual honeypot daemon,” 10th dfn-cert workshop, hamburg, germany. vol. 2, 2003.
Y. T. Abewa and S. Z. Melese, “Dynamic Interactive Honeypot for Web Application Security,” International Journal of Wireless and Microwave Technologies, vol. 14, no. 6, pp. 1-14, 2024.
T. Luo, Z. Xu, X. Jin, Y. Jia and X. Ouyang, “Iotcandyjar: Towards an intelligent-interaction honeypot for IoT devices,” Black Hat, vol. 1, pp. 1-11. 2017.
T. Yagi, N. Tanimoto, T. Hariu and M. Itoh, “Enhanced attack collection scheme on high interaction web honeypots,” The IEEE symposium on Computers and Communications, Riccione, Italy, pp. 81-86, 2010.
S. Fatima1, S. Luqmaan and N. A. Rasheed, “Web scraping with python and selenium,” IOSR Journal of Computer Engineering (IOSRJCE) vol. 23, no. 3, pp.1-5, 2021.
A. Vaswani et al., “Attention is all you need,” 31st Conference on Neural Information Processing Systems (NIPS 2017), Long Beach, CA, USA., 2017.
M. Freitag and Y. Al-Onaizan, “Beam search strategies for neural machine translation,” arXiv preprint arXiv:1702.01806, 2017.
V. Mnih, K. Kavukcuoglu, D. Silver, A. Graves, I. Antonoglou, D. Wierstra and M. Riedmiller, “Human-level control through deep reinforcement learning,” Nature, vol. 518, no. 7540, pp. 529–533, Feb. 2015.
B. O’Donoghue, I. Osband, R. Munos and V. Mnih, “The uncertainty Bellman equation and exploration,” in Proceedings of the 35th International Conference on Machine Learning, Stockholm, Sweden, 2018.
P. Lanka, K. Gupta and C. Varol, “Intelligent Threat Detection—AI-Driven Analysis of Honeypot Data to Counter Cyber Threats,” Electronics, vol. 13, no. 13, p.2465, 2024.
J. D. Guarnizo et al., “SIPHON: Towards Scalable High-Interaction Physical Honeypots,” Proceedings of the 3rd ACM Workshop on CyberPhysical System Security, pp. 57-68, 2017.
A. Vetterl and R. Clayton, “Honware: A Virtual Honeypot Framework for Capturing CPE and IoT Zero Days,” 2019 APWG Symposium on Electronic Crime Research (eCrime), Pittsburgh, PA, USA, pp. 1-13, 2019.
M. Yamamoto, S. Kakei and S. Saito, “FirmPot: A Framework for Intelligent-Interaction Honeypots Using Firmware of IoT Devices,” 2021 Ninth International Symposium on Computing and Networking Workshops (CANDARW), Matsue, Japan, pp. 405-411, 2021.
K. Shivam1, M. Raval, N. Nrip and A. Sinha, “A research study on Web Application Security,” International Journal of Multidisciplinary Research Transactions, vol. 4, no. 6, pp. 93-104, 2022.
X. Glorot, A. Bordes and Y. Bengio, “Deep sparse rectifier neural networks,” in Proceedings of the 14th International Conference on Artificial Intelligence and Statistics (AISTATS 2011), pp. 315–323, 2011.
M. Wadhwa, X. Zhao, J. J. Li and G.Durrett, “Learning to Refine with Fine-Grained Natural Language Feedback,” arXiv preprint arXiv:2407.02397, 2025.
H. S. Annapurna and S. Devi, “Machine learning-based adaptive equalization with software-defined radio experimental setup,” ECTI Transactions on Computer and Information Technology (ECTI-CIT), vol. 19, no. 2, pp. 271–281, 2025.