DSSF: Decision Support System to Detect and Solve Firewall Rule Anomalies based on a Probability Approach
Main Article Content
Abstract
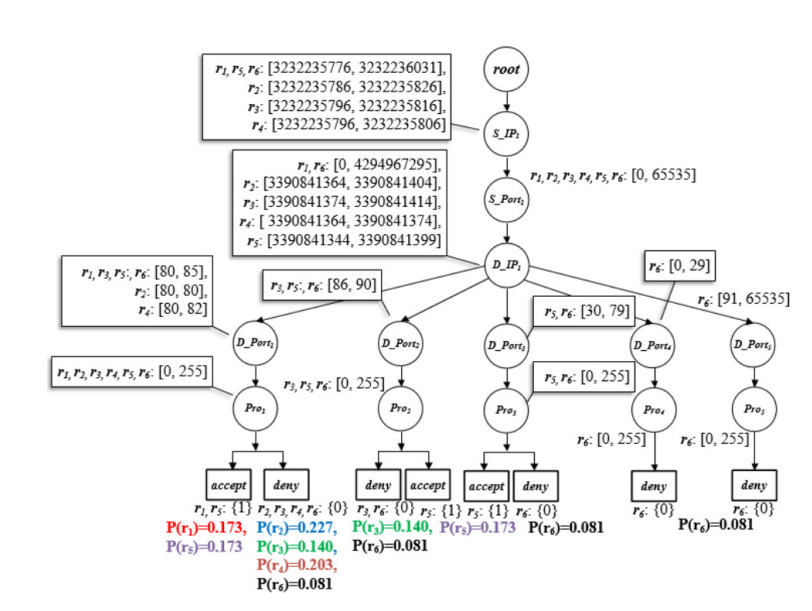
Currently, establishing a private network on the Internet is highly hazardous for attacks as attackers continuously scan computers for vulnerabilities within the connected network. The firewall ranked the highest as a network device is selected to protect unauthorized accesses and attacks. However, firewalls can effectively protect against assaults based on adequately defined rules without any anomalies. In order to resolve anomaly problems and assist firewall admins with the ability to manage the rules effectively, in this paper, a prototype of the decision support system has been designed and developed for encouraging admins to optimize firewall rules and minimize deficiencies that occur in rules by using the probability approach. The experimental results clearly show that the developed model encourages experts and administrators of firewalls to make significant decisions to resolve rule anomalies by expert's confidence increases by 14.8 %, and administrators' confidence soars similarly about 44.2 %. Lastly, the accuracy of correcting rule anomalies is 83 %.
Article Details

This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.
References
E. S. Al-Shaer and H. H. Hamed, Modeling and Management of Firewall Policies, in IEEE Transactions on Network and Service Management, vol. 1, no. 1, pp. 2-10, 2004.
S. Khummanee, The semantics loss tracker of firewall rules, in IC2IT 2018 Recent Advances in Information and Communication Technology, vol. 769, pp. 220{231, 2018.
E. Al-Shaer, H. Hamed, R. Boutaba and M. Hasan, Conflict classification and analysis of distributed firewall policies, in IEEE Journal on Selected Areas in Communications, vol. 23, no. 10, pp. 2069-2084, 2005.
A. X. Liu, Formal Verification of Firewall Policies, 2008 IEEE International Conference on Communications, pp. 1494-1498, 2008.
S. Khummanee, A. Khumseela and S. Puangpronpitag, Towards a new design of firewall: Anomaly elimination and fast verifying of firewall rules, The 2013 10th International Joint Conference on Computer Science and Software Engineering (JCSSE), pp. 93-98, 2103.
M. Rezvani and R. Aryan, Analyzing and resolving anomalies in firewall security policies based on propositional logic, 2009 IEEE 13th International Multitopic Conference, pp. 1-7, 2009.
H. Hu, G. Ahn and K. Kulkarni, Detecting and Resolving Firewall Policy Anomalies, in IEEE Transactions on Dependable and Secure Computing, vol. 9, no. 3, pp. 318-331, 2012.
Mell, P.M., Scarfone, K.A., Romanosky, S., A complete guide to the common vulnerability scoring system version 2.0, The National Institute of Standards and Technology (NIST). Accessed 15 Aug 2019.
Wool, A., Architecting the Lumeta firewall analyzer, In SSYM’01: Proceedings of the 10th conference on USENIX Security Symposium, pp. 7, 2001.
A. Mayer, A. Wool and E. Ziskind, Fang: a firewall analysis engine, Proceeding 2000 IEEE Symposium on Security and Privacy, pp. 177-187, 2000.
A. Hari, S. Suri and G. Parulkar, Detecting and resolving packet filter conflicts, Proceedings IEEE INFOCOM 2000. Conference on Computer Communications. Nineteenth Annual Joint Conference of the IEEE Computer and Communications Societies (Cat. No.00CH37064), pp. 1203-1212 vol.3, 2000.
L. Zhang and M. Huang, A Firewall Rules Optimized Model Based on Service-Grouping, 2015 12th Web Information System and Application Conference (WISA), pp. 142-146, 2015.
Lihua Yuan, Hao Chen, Jianning Mai, Chen-Nee Chuah, Zhendong Su and P. Mohapatra, FIREMAN: a toolkit for firewall modeling and analysis, 2006 IEEE Symposium on Security and Privacy, pp. 15 pp.-213, 2006.
A. Sa^adaoui, N. B. Y. B. Souayeh and A. Bouhoula, Formal approach for managing firewall misconfigurations, 2014 IEEE Eighth International Conference on Research Challenges in Information Science (RCIS), pp. 1-10, 2014.
W. Krombi, M. Erradi and A. Khoumsi, Automata-based approach to design and analyze security policies, 2014 Twelfth Annual International Conference on Privacy, Security and Trust, pp. 306-313, 2014.
A. Saadaoui, N. B. Y. B. Souayeh and A. Bouhoula, Automated and Optimized FDDBased Method to Fix Firewall Misconfigurations, 2015 IEEE 14th International Symposium on Network Computing and Applications, pp. 63-67, 2015.
Aggarwal, C.C., Neural Networks and Deep Learning, 1 ed. Springer International Publishing, Boca Raton, FL, USA, 2018.
Morris, D., Koning, M., Bayes’ Theorem Examples: A Visual Introduction For Beginners. Blue Windmill Media, 80 Strand, London, WC2R 0RL UK, 2016.
Berry, K.J., Johnston, J.E., Paul W. Mielke, J., The Measurement of Association: A Permutation Statistical Approach. Springer International Publishing, Springer Nature Switzerland AG, 2018.
Ting, K.M., Confusion Matrix. In: Sammut, C., Webb, G.I. (eds.) Encyclopedia of Machine Learning. pp. 209-209. Springer US, Boston, MA, 2010.
CelPlan Technologies, I., GPP QoS Class Identification QCI categories. http://www.celplan.com (2019). Accessed 12 Sep 2019
Python Software Foundation, Python 3.8.7. https://www.python.org/downloads/release/python-387/ (2019). Accessed 10 Feb 2020
Python Software Foundation, Python bindings for the Qt cross platform application toolkit. https://pypi.org/project/PyQt5/ (2019). Accessed 12 Aug 2020