Electromagnetic Side-Channel Attack on AES using Low-end Equipment
Main Article Content
Abstract
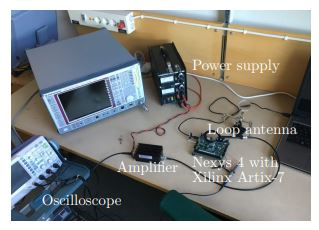
Side-channel attacks on cryptographic algorithms targets the implementation of the algorithm. Information can leak from the implementation in several different ways and, in this paper, electromagnetic radiation from an FPGA is considered. We examine to which extent key information from an AES implementation can be deduced using a low-end oscilloscope. Moreover, we examine how the antenna's distance from the FPGA affects the results in this setting. Our experiments show that some key bits indeed can be inferred from the measurements, despite having a far from optimal setting.
Article Details

This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.
References
N. I. of Standards and Technology, “Advancedencryption standard,” NIST FIPS PUB 197,2001.
P. Kocher, J. Jaffe, and B. Jun, “Differential power analysis,” in Advances in CryptologyCRYPTO99, ser. LNCS, M. Wiener, Ed.,vol.1666. Springer-Verlag, 1999, pp. 388-397.
P. C. Kocher, “Timing attacks on implementations of diffe-hellman, rsa, dss, and other systems,” in Annual International Cryptology Conference. Springer, 1996, pp. 104-113.
D. Brumley and D. Boneh, “Remote timing attacks are practical,” Computer Networks, vol. 48, no. 5, pp. 701-716, 2005.
D. Genkin, A. Shamir, and E. Tromer, “Rsakey extraction via low-bandwidth acoustic cryptanalysis,” in Annual Cryptology Conference.Springer, 2014, pp. 444-461.
M. Backes, M. D¨urmuth, S. Gerling, M. Pinkal, and C. Sporleder, “Acoustic side-channel attacks on printers,” in USENIX Security symposium, 2010, pp. 307-322.
J. Brouchier, T. Kean, C. Marsh, and D. Naccache, “Temperature attacks,” IEEE Security &
Privacy, vol. 7, no. 2, pp. 79-82, 2009.
M. Hutter and J.-M. Schmidt, “The temperature side channel and heating fault attacks,” in International Conference on Smart Card Research and Advanced Applications. Springer, 2013, pp.219-235.
D. Boneh, R. A. DeMillo, and R. J. Lipton, “On the importance of checking cryptographic protocols for faults,” in International conference on the theory and applications of cryptographic techniques. Springer, 1997, pp. 37-51.
M. Joye, A. K. Lenstra, and J.-J. Quisquater, “Chinese remaindering based cryptosystems in
the presence of faults,” Journal of cryptology, vol. 12, no. 4, pp. 241-245, 1999.
J.-J. Quisquater and D. Samyde, “Electromagnetic analysis (ema): Measures and countermeasures for smart cards,” in International Conference on Research in Smart Cards. Springer, 2001, pp. 200-210.
A. Dehbaoui, V. Lomne, P. Maurine, L. Torres, and M. Robert, “Enhancing electromagnetic
attacks using spectral coherence based cartography,” in IFIP/IEEE International Conference
on Very Large Scale Integration-System on a Chip. Springer, 2009, pp. 135-155.
A. Kerckhoffs, “La cryptographie militaire. (French) [Military cryptography],” Journal des
Sciences Militaires, vol. IX, pp. 5-83, Jan. 1883.
Y. Hori, T. Katashita, A. Sasaki, and A. Satoh, “Electromagnetic side-channel attack against 28- nm fpga device,” Pre-proceedings of WISA, 2012.
T. S. Messerges, E. A. Dabbish, and R. H. Sloan, “Investigations of power analysis attacks
on smartcards,” Smartcard, vol. 99, pp. 151-161, 1999.
S. Mangard, E. Oswald, and T. Popp, Power Analysis Attacks: Revealing the Secrets of
Smart Cards (Advances in Information Security). Berlin, Heidelberg: Springer-Verlag, 2007.
E. De Mulder, “Electromagnetic techniques and probes for side-channel analysis on cryptographic devices,” Diss. PhD Thesis, 2010.
K. Gandolfi, C. Mourtel, and F. Olivier, “Electromagnetic analysis: Concrete results,” in In- Electromagnetic Side-Channel Attack on AES using Low-end Equipment 147 ternational workshop on cryptographic hardware and embedded systems. Springer, 2001, pp. 251- 261.
J. Daemen and V. Rijmen, The Design of Rijndael: AES - The Advanced Encryption Standard. Berlin, Heidelberg, New York: Springer Verlag, 2002.
W. Aerts, E. De Mulder, B. Preneel, G. A. E. Vandenbosch, and I. Verbauwhede, “Dependence of rfid reader antenna design on read out distance,” IEEE Transactions on Antennas and Propagation, vol. 56, no. 12, pp. 3829-3837, Dec 2008.
F. Durvaux, M. Renauld, F.-X. Standaert, L. van Oldeneel tot Oldenzeel, and N. VeyratCharvillon, “Effcient removal of random delays from embedded software implementations using hidden markov models,” in Smart Card Research and Advanced Applications, S. Mangard, Ed. Berlin, Heidelberg: Springer Berlin Heidelberg, 2013, pp. 123-140.
D. Strobel and C. Paar, “An effcient method for eliminating random delays in power traces of embedded software,” in Information Security and Cryptology - ICISC 2011, H. Kim, Ed. Berlin, Heidelberg: Springer Berlin Heidelberg, 2012, pp. 48-60.
J. G. J. van Woudenberg, M. F. Witteman, and B. Bakker, “Improving differential power analysis by elastic alignment,” in Topics in Cryptology -CT-RSA 2011, A. Kiayias, Ed. Berlin, Heidelberg: Springer Berlin Heidelberg, 2011, pp.104- 119.
J. L. Massey, “Guessing and entropy,” in Proceedings of the 1994 IEEE International Symposium on Information Theory, 1994, p. 204.
E. De Mulder, S. Ors, B. Preneel, and I. Verbauwhede, “Differential electromagnetic attack on an fpga implementation of elliptic curve cryptosystems,” in 2006 World Automation Congress. IEEE, 2006, pp. 1-6.
E. De Mulder, P. Buysschaert, S. Ors, P. Delmotte, B. Preneel, G. Vandenbosch, and I. Verbauwhede, “Electromagnetic analysis attack on an fpga implementation of an elliptic curve cryptosystem,” in EUROCON 2005-The International Conference on “Computer as a Tool”, vol. 2. IEEE, 2005, pp. 1879-1882.
V. Carlier, H. Chabanne, E. Dottax, and H. Pelletier, “Electromagnetic side channels of an fpga implementation of aes,” in Cryptology eprint archive, report 2004/145. Citeseer, 2004.
E. Brier, C. Clavier, and F. Olivier, “Correlation power analysis with a leakage model,” in International Workshop on Cryptographic Hard ware and Embedded Systems. Springer, 2004, pp. 16-29.
Y. Hori, T. Katashita, A. Sasaki, and A. Satoh, “Sasebo-giii: A hardware security evaluation
board equipped with a 28-nm fpga,” in The 1st IEEE Global Conference on Consumer Electronics 2012. IEEE, 2012, pp. 657-660.
J. Danial, D. Das, S. Ghosh, A. Raychowdhury, and S. Sen, “Scniffer: Low-cost, automated, effcientelectromagnetic side-channel sniffng,” arXiv preprint arXiv:1908.09407, 2019.
G. Hospodar, B. Gierlichs, E. De Mulder, I. Verbauwhede, and J. Vandewalle, “Machine learning in side-channel analysis: a first study,” Journal of Cryptographic Engineering, vol. 1, no. 4, p. 293, 2011.
P. Robyns, P. Quax, and W. Lamotte, “Improving cema using correlation optimization,” IACR Transactions on Cryptographic Hardware and Embedded Systems, vol. 2019, pp. 1-24, 2018.
S. Chari, J. R. Rao, and P. Rohatgi, “Template attacks,” in International Workshop on
Cryptographic Hardware and Embedded Systems. Springer, 2002, pp. 13-28.
J. Xu, Y. Tang, Y.Wang, and X.Wang, “A practical side-channel attack of a lorawan module using deep learning,” in 2019 IEEE 13th International Conference on Anti-counterfeiting, Security, and Identification (ASID), 2019, pp. 17-21.
M. Carbone, V. Conin, M.-A. Corn´elie, F. Dassance, G. Dufresne, C. Dumas, E. Prouff, and
A. Venelli, “Deep learning to evaluate secure rsa implementations,” IACR Transactions on Cryptographic Hardware and Embedded Systems, vol. 2019, no. 2, pp. 132-161, Feb. 2019.
Y. Zhou and F.-X. Standaert, “Deep learning mitigates but does not annihilate the need of aligned traces and a generalized resnet model for side-channel attacks,” Journal of Cryptographic Engineering, 04 2019.
S. Jin, S. Kim, H. Kim, and S. Hong, “Recent advances in deep learning-based side-channel analysis,” ETRI Journal, vol. 42, no. 2, pp. 292-304, 2020.
D. Das, M. Nath, B. Chatterjee, S. Ghosh, and S. Sen, “Stellar: A generic em side-channel attack protection through ground-up root-cause analysis,” in Proc. 2019 IEEE Int. Symp. Hardw. Oriented Security Trust, 2019.
H. Ma, J. He, Y. Liu, Y. Zhao, and Y. Jin, “Cad4em-p: Security-driven placement tools for electromagnetic side channel protection,” in 2019 Asian Hardware Oriented Security and Trust Symposium (AsianHOST). IEEE, 2019, pp. 1-6.