A Large Scalar Multiplication Algorithm using Modified Pell Numbers for Key Generation
Main Article Content
Abstract
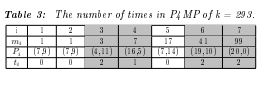
Cryptographic algorithms consist of two parts, a key and an algorithm, to encrypt and decrypt data. The key is an essential part that works with the algorithm. The security of encryption schemes depends on the key size (key length) and the longer the key, the better the security it provides. Applying an elliptic curve has for key agreement provides a high-performance architecture and high security. The main process for calculating key points in Elliptic Curve Cryptography (ECC) is called scalar multiplication, which relates to point addition and point doubling. An efficient algorithm, proposed as the Large Scalar Multiplication Algorithm using Modified Pell Numbers (LSMA-MPN), was introduced to speed up the calculation of points on elliptic curves during large scalar multiplications. This system also reduced computation time by applying Modified Pell numbers in a 22 matrix representation. The experimental results showed that computation time was reduced by approximately 67% in comparison with the computation time required by a general algorithm.
Article Details

This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.
References
C. Easttom, "Modern Cryptography: Applied Mathematics for Encryption and Information Security," McGraw-Hill Education, October 2015.
C. Paar, and J. Pelzl, "Understanding Cryptography," Springer Heidelberg Dordrecht London New York, 2010.
B. AlBelooshi, E. Damiani, K. Salah, and T. Martin, "Securing Cryptographic Keys in the Cloud: A Survey," The IEEE Computer Society, IEEE Cloud Computing, pp. 42-56, 2016.
A. Gupta, et al., "Prevailing and emerging cyber threats and security practices in IoT-Enabledsmart grids: A survey," in the Journal of Network and Computer Applications, Vol. 132, April 15, pp. 118-148, 2019.
Y. Li, et al., "Intelligent cryptography approach for secure distributed big data storage in cloud computing," Information Sciences 387, pp. 103-115, 2017.
W. Stallings, "Cryptography and Network Security: Principles and Practice, Global Edition," Pearson Education Limited, October 11, 2016
B. Schneier, "Applied Cryptography: Protocols, Algorithms, and Source Code in C," John Wiley & Sons Inc, New York, United States, November 1, 1995.
S. Y. Yan, "Computational Number Theory and Modern Cryptography, First Edition," Higher Education Press, November 27, 2012.
V. S. Miller, "Use of elliptic curves in cryptography. in Wiliams, H.C. (ed.) Advances in Cryptology – CRYPTO ’85, volume 218 of Lecture Notes in Computer Science, Springer, pp. 417–426, 1985.
F. Akhter, "Faster Scalar Multiplication Algorithm to Implement a Secured Elliptic Curve Cryptography System," International Journal of Advanced Computer Science and Applications, Vol. 7, No. 1, pp. 639-644, 2016.
A. Overmars and S. Venkatraman, "A New Method of Golden Ratio Computation for Faster Cryptosystems," Proceeding of 2017 Cybersecurity and Cyberforensics Conference (CCC), pp. 9–15, 2017.
J. J. Bravo, P. Das, S. Guzman, and S. Laisham, "Powers in products of Terms of Pell's and Pell-Lucus Sequences," Indian Statistical Institute, Delhi Centre, New Delhi, India, pp.1-10, 2010.
A. F. Horadam, "Applications of Modified Pell Numbers to Representations," Ulam Quaterly, Vol. 3, No. 1, pp. 34 - 53, 1994.
V. W. de Spinadel, "The metallic means family and renormalization group techniques," Trudy Inst. Mat. i Mekh. UrO RAN, Vol. 6, No. 1, pp. 173–189, 2000.
U. Priyatharsan, P. L Rupasinghe, and I. Murray, "A New Elliptic Curve Cryptographic System over the Finite Fields," Proceeding of the 6th National Conference on Technology and Menagement (NCTM), pp. 164-169, 2017.
R. Harkanson and Y. Kim, "Applications of Elliptic Curve Cryptography A light introduction to elliptic curves and a survey of their applications," Proceeding of the 12th Annual Conference on Cyber and Information Security Research (CISRC), pp. 1-7, 2017.
N. Koblitz, "Elliptic curve cryptosystems," Mathematics of Computation, Vol. 48, No. 177, pp. 203-209, 1987.
K. Gupta and S. Silakari, "ECC over RSA for Asymmetric Encryption: A Review," IJCSI International Journal of Computer Science Issues, Vol. 8, Issue 3, No. 2, 2011, pp. 370-375.
M. Alam, I. Jahan, L. J. Rozario, and I. Jerin, “A Comparative Study of RSA and ECC and Implementation of ECC on Embedded Systems”, International Journal of Innovative Research in Advanced Engineering (IJIRAE), Vol. 3, Issue 3, pp. 86-93, 2016.
B. Akanksha, and A. Arun,"Providing Security, Integrity and Authentication Using ECC Algorithm in cloud storage," Proceeding of the 2017 International Conference on Computer Communication and Informatics (ICCCI), pp. 1-5, 2017.
S. Gajbhiye, S. Karmakar, and M. Sharma, "Study of Finite Field over Elliptic Curve: Arithmetic Means," In the International Journal of Computer Applications, Vol. 47, No.17, pp. 32-38, 2012.
T. S. Mathew and S. Suresh, "Comparative Analysis of AES and ECC in Automated Metering Infrastructure," Proceeding of the 2017 international Conference on Wireless Communications, Signal Processing and Networking (WiSPNET), pp. 934-938, 2017.
D. R. Susantio and I. Muchtadi-Alamsyah, "Implementation of Elliptic Curve Cryptography in Binary Field," Journal of Physics: Conference Series, Vol. 710, pp. 1-9, 2016.
K. Phalakarn, K. Phalakarn, and V. Suppakitpaisarn, "Optimal Representation for Right-to-Left Parallel Scalar and Multi-Scalar Point Multiplication," International Journal of Networking and Computing, Vol. 8, No. 2, pp. 166-185, 2018.
D. Khleborodov, "Fast elliptic curve point multiplication based on window Non-Adjacent Form method," Applied Mathematics and Computation, Vol. 334, pp. 41–59, 2018.
M. M. Panchbhai and U. S. Ghodeswar, "Implementation of Point Addition $&$ Point Doubling for Elliptic Curve," Proceeding of International Conference on Communication and Signal Processing, pp. 746-749, 2015.
K. Javeed, X. Wang, and M. Scott, "High performance hardware support for elliptic curve cryptography over general prime field," Microprocessors and Microsystems, No. 50, pp. 331–342, 2017.
A. J. Raphael and V. Sundaram, "Secured Communication through Fibonacci Numbers and Unicode Symbols," International Journal of Scientific & Engineering Research, Vol. 3, Issue 4, pp. 1-5, 2012.
M. Mukherjee and D. Samanta, "Fibonacci Based Text Hiding Using Image Cryptography," Lecture Notes on Information Theory, Vol. 2, No. 2, pp. 172-176, 2014.
P. Agarwal, N. Agarwal, and R. Saxena, "Data Encryption through Fibonacci Sequence and Unicode Characters," International Journal of Computer Science and Information Technology, Vol. 5, No. 2, pp. 79-82, 2015.
N. Zhang and S. Tan, "Elliptic Curve Scalar Multiplication Based on Fibonacci Number," Proceeding of 5th International Conference on Intelligent Networking and Collaborative Systems, pp. 507-510, 2013.
S. Liu, G. Qi and X. A. Wang, "Fast and Secure Elliptic Curve Scalar Multiplication Algorithm Based on a Kind of Deformed Fibonacci-type Series," in Proceedings of 2015 10th International Conference on P2P, Parallel, Grid, Cloud and Internet Computing, pp. 398-402, 2015.
F. Duemong, L. Preechaveerakul,"Applying Pell Numbers for Efficient Elliptic Curve Large Scalar Multiplication," Proceeding of the 22nd International Computer Science and Engineering Conference (ICSEC), pp. 204-207, 2018.